Engineering student Hemanth Joseph, who bypassed Apple's activation lock, is now the poster boy for a young community of ethical hackers. Nikita Puri reports.

For the past few days, Hemanth V Joseph finds himself pausing before he answers an unknown phone number, or even when he gets a new message on Facebook.
Ever since Joseph blogged about how he bypassed tech giant Apple's iPad activation lock, requests to unlock iPhones, iPads and iPods have been pouring in from Sri Lanka, Nepal, Pakistan and the United States.
The 21 year old is a final year student of mechanical engineering at the Amal Jyothi Engineering College, Kanjirappally, Kerala.
Keeping up with the ever-evolving cyberspace and exposing its vulnerabilities is "just an interest" Joseph has developed over the last three-odd years.
It was when he was studying biosciences in junior college that Joseph found himself inexplicably drawn to how Web applications work, and began teaching himself programming languages.
"My friends call me a lot of bad words now," says Joseph, "They say they can't go home because of me: Their parents call them and ask what they are doing when a boy from their class is making so much news."
Before Joseph bypassed iPad's security, he made headlines for exposing a critical vulnerability in Google's Cloud Platform (used by end-users to build applications, store and analyse data).
Not only did this get him listed in Google's Hall of Fame honouring ethical hackers, it also won him a bounty of $7,500 (about Rs 5,00,000).
He's won $9,500 (about Rs 6,40,00) from AT&T before, Yahoo has given him $5,000 (about Rs 3,40,000), and he's got $2,000 (about Rs 1,30,500) from Pebble Smartwatch, besides others.
From BlackBerry to Twitter, Joseph has been listed in several Halls of Fame over the last four years. "It's good pocket money," he says, chuckling.
Joseph has never reconsidered his decision not to formally study computer science.
He uses the case of a falling raindrop to explain his fascination for mechanical engineering: "Just think, without friction in the air, a raindrop would accelerate so much that when it hits the ground, it would have the velocity of two or three times of a bullet. Mechanical engineering explains natural phenomenon, it helps explain everything around you."
He considers his recent feat with Apple particularly significant because Apple's security is considered to be the very best.
"My dad and I usually use Apple products, so he (Joseph) showed me how he bypassed iPad's security," says his college friend Evan Thomas.
After the feat, Thomas remembers Joseph telling him: "Kando, security itre ollu." That's Malayalam for "see, this is all the security there is."
Joseph had bought a second-hand iPad Air from eBay when a developer-friend of his needed one to test applications. But when the device arrived, Joseph found it locked.
This is a security measure designed to keep your data safe as it cannot be reactivated without a password.
Most would find only two ways out of this: Contact the previous owner, or approach customer care for assistance. But Joseph confesses to enjoy "being put in difficult situations" so that he can find a way out.
So, despite being new to Apple's iOS operating system, he applied what many would call a blunt-force method to bypass the system.
He used the 'Lost Mode' option to put the device into activation mode. But logging in requires an Internet connection, and that's when Joseph chose 'other network' and then WPA2 Enterprise.
Next, he realised there was no character limit in the blanks to be filled, so he put in thousands of characters.
This effectively froze the screen, but he wasn't in. He tried it again, this time using iPad's magnetic smart case to cover the screen once he had frozen it.
Then Joseph found himself looking at the home screen. He had bypassed the activation security.

Whether Joseph received any cash reward from Apple remains a secret he's not spilling any time soon.
Tech giants have often been known not to publicise such findings, and such incidents are usually reported by bounty hunters themselves.
In this case, Joseph blogged about it in late November (www.hemanthjoseph.com) after a security update had been put in place. His blog also has screenshots of his conversation with Apple's product security team and a video showing the bypass process.
"When we ask him to go to sleep at night, he says he can't because he's looking for bugs," says Thomas, who shares a flat with Joseph.
"Our college has high-speed Internet so he looks for bugs even when classes are on. The professors also let him be, thinking he's working on something important. If he's stuck somewhere, he'll ask for help but he doesn't give up," adds Thomas.
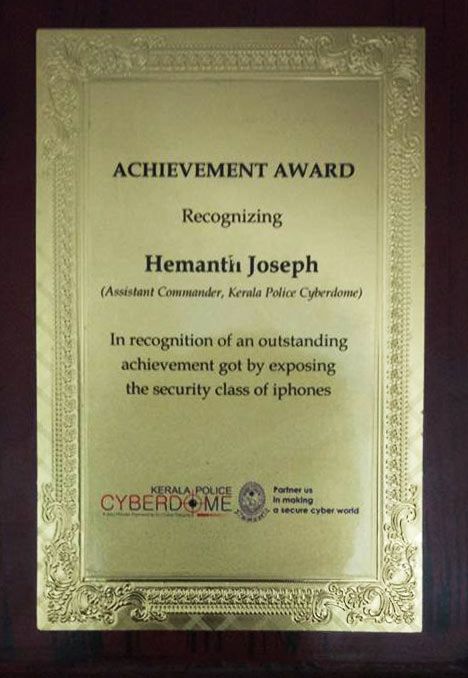
Over the last few months, Joseph has also been working with Cyberdome, a public-private partnership initiated by the Kerala police to combat cyber crime.
"We work with volunteers and have a lot of senior professionals on board, so we were very doubtful about recruiting youngsters," says Manoj Abraham, inspector general of police, Thiruvananthapuram, and Cyberdome's nodal officer.
But over the past few months, Abraham has seen "youngsters like Hemanth" find solutions to the newer challenges that stump even those with "more experience".
"We've seen a huge success rate with this partnership. Now we can respond better when Web sites are hacked," he says, adding, "In the last six months, piracy of Malayalam films has become almost nil."
Megastar Mohanlal's Pulimurugan is a recent beneficiary.
Hemanth may be young, but his age has no bearing on his confidence, expertise or brilliance, believes Abraham, adding, "He's one of our brightest stars."
For Abraham, Joseph represents a generation of problem-solving youngsters who tackle cyber issues "in a matter of minutes."
Realising the need for white hat hackers, Joseph and his friends have founded 0SecCon, India's first open security community for students.
"India only has professional conferences. There's nothing for students or beginners. We want to bridge that gap and teach students the very basics, all for free," he says.
"We are reaching a phase where our cooking devices will tell us how to cook and whether we've over-boiled food," Joseph says. "Anything connected to the Internet is vulnerable to hack. We must be prepared to defend ourselves."










