Have you noticed that these virus times have altered the look of your inbox?
Is it packed with spam mails from Yoyo Yans offering to send masks to your doorstep? Or Rita ready and eager to export to you everything from diagnostic kits and ventilators to forehead thermometers and gowns?
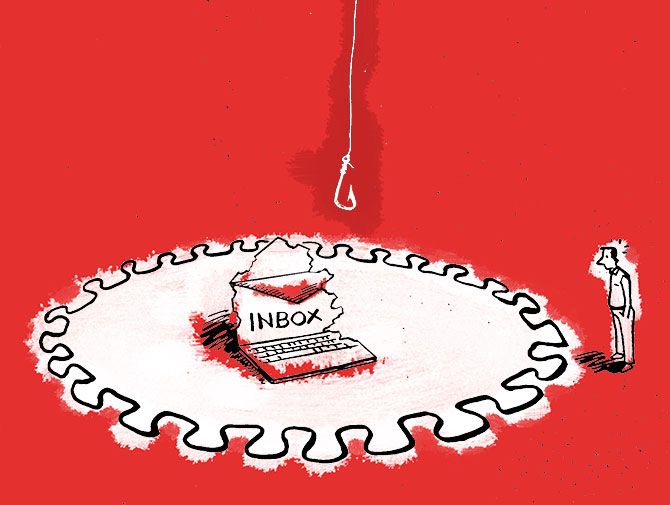
While the virus out there is meddling big-time with our precious lives, the danger is lurking in our email boxes too.
Bigger than spam is the phishing rackets currently afoot.
Venkata Satish Guttula lays out the dangers lurking within your laptop.
Illustration: Dominic Xavier/Rediff.com
Novel CoronaVirus is not only posing a grave danger in the real world, but it is also a threat to the cyberworld.
Cybercriminals are using this time to exploit public fears about this deadly virus using phishing attacks.
Phishing is a technique used by cybercriminals to send genuine-looking emails and make the user take actions. These actions can be replying with personal information or clicking the link in the email and doing some transactions etc.
One such scenario is: A user receives an email from someone impersonating as the income tax department saying that the user has a tax refund. The user can transfer that refund to his account by clicking on the link that is provided in the email and just give the bank account and login details on the page.
This page will look like the income tax department's page. But it is not. And the user's details are compromised. Money is siphoned off from the bank using these details.
The COVID-19 situation has sparked off a ‘trend’ of many users receiving phishing emails from crooks impersonating as a software/antivirus company, who obviously have the time right now to create more evil. The mails say that they are offering their free software to use to work from home. This software can contain malware or malicious software when installed and will infect the computer.
Some types of malware
Ransomware: Once infected, this malware can encrypt documents in the computer and demand a ransom in the form of Bitcoins to decrypt the files.
Keylogger: This malware can record whatever the user is typing, including the login credentials for a bank or an email account, and send it to the hacker.
Remote Access Trojan or RAT: This malware can give full remote access of the infected computer to a hacker. This hacker can watch what the user is browsing, or he can remotely activate the web camera and watch, or he can read the documents on the computer.
Zombies or bots: This malware, even though it is harmless to the computer, can control it remotely to participate in the Distributed Denial of Service (DDOS) attacks to bring down the websites or networks.
Other examples of phishing emails based on COVID-19
- An email impersonating as HR of the company asking users to review the work from home policy, in the attached (malicious) word file.
- An email impersonating as HR that a colleague has tested COVID-19 positive and to check the attached (malicious) document on how to keep safe from the virus.
- An email impersonating as the CEO of the company asking an employee to join in a video conference by clicking on the link provided. This link can download malware.
- An email impersonating as an IT help desk, asking users to download and install the (malicious) VPN software for work from home.
- An email impersonating as the health department asking users to install (malicious) software on their mobile phones.
Tips to prevent yourself from being a victim to the phishing attacks
- Beware of online requests for personal information: A coronavirus-themed email that seeks personal data like your bank login information is a phishing scam. Never respond to the email with your bank login details or any other personal data of yours.
- Check the email address or link: Always check the ‘from’ address to see if the email is sent from your organisation or your bank. Also, check the links in the email if they point to the actual domain.
- Watch for spelling and grammatical mistakes: Check for spelling and grammatical errors to determine if the email is a phishing email or not. More of these errors indicate it is.
- Be suspicious of emails that insist you act now: Phishing emails create a sense of urgency and demand immediate action. They want you to click on a link, and provide personal information right there and then or make you do a financial transaction. If the email looks genuine, call the person for confirmation and then act.
- Backup: Always backup your data either in the CVS, GIT, on cloud or external drive.
Venkata Satish Guttula is director, security, with Rediff.com. He can be contacted on venkatas@rediff.co.in.










