Photographs: Jim Urquhart/Reuters Vicky Nanjappa
Campaign targeted the critically important infrastructure of engineering firms, government organisations, banks and universities in the Middle East, says Rediff.com's Vicky Nanjappa.
During the year 2012 the most significant of the cyber espionage incidents were related to the activity of Madi, Gauss and Flame malware, which were distributed primarily in the Middle East. One campaign related to penetrating computer systems went on for almost a year and targeted users primarily in Iran, Israel and Afghanistan.
The malicious program was named "Madi" based on the strings and identifiers used by the cybercriminals in their malware. The malicious components were distributed via attacks that were based on a set of well-known unsophisticated technologies. This indicates that the victims' awareness of Internet security left much to be desired.
These attacks involved installing backdoors coded in Delphi on victim machines. They could have been created by an amateur programmer or else by a professional developer who was extremely short of time. The campaign targeted the critically important infrastructure of engineering firms, government organisations, banks and universities in the Middle East.
Victims were chosen among users within these organisations whose communications had been under close surveillance for extended periods of time. The Gauss malware was discovered in the course of an investigation initiated by the International Telecommunication Union after the discovery of the Flame malware.
...
Madi, Gauss, Flame: Year's most sophisticated malware
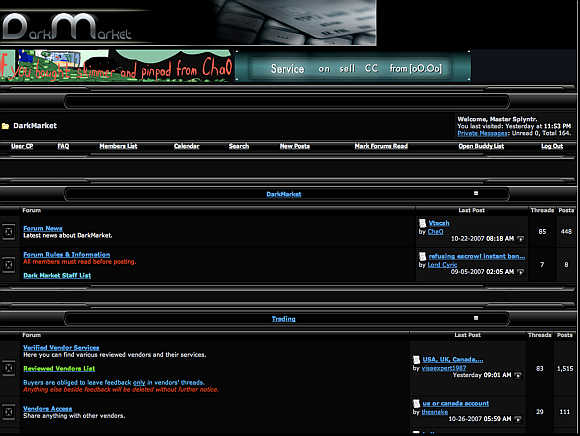
Image: This Federal Bureau of Investigation computer screen image shows an online forum called 'Dark Market' where it educates users where to buy skimming devices to penetrate bank accounts, how to distribute malware through spam, and buy stolen credit cards among other things.Photographs: Handout/Reuters
Essentially, Gauss is a nation-state sponsored "banking" Trojan. In addition to stealing a variety of data from infected Windows machines, it includes malicious payload which is encrypted and the purpose of which is not yet known.
The malicious program activates only on systems with certain configurations. Gauss is based on the Flame platform and shares some features with Flame, such as routines for infecting USB drives. A study conducted by Kaspersky Lab states that the development of code for C&C servers based on the platform began as far back as December 2006.
Judging by the comments left in the source code, the project was developed by at least four programmers. The C&C code supports three communication protocols. A major finding is that it handles requests from four malicious programs, codenamed by the authors as SP, SPE, FL and IP.
Of these four malicious programs, only two are known at this time: Flame and SPE (aka miniFlame). Android 2.3.6 "Gingerbread", which accounts for 28 per cent of all blocked attempts to install malware, was the most commonly attacked version. It is not new: it was released in September 2011.
However, due to the considerable segmentation of the Android device market, it remains one of the most popular versions.
...
Madi, Gauss, Flame: Year's most sophisticated malware
Image: Online attacks primarily involve various exploits.Photographs: Handout/Reuters
There are significant differences between the diagrams: in 48 per cent of all cases victims of cybercriminals used Gingerbread, which was installed on 55 per cent of all devices, while in 43 per cent of all cases the victims had Ice Cream Sandwich, the latest version of Android OS, which is installed on 23.7 per cent of all devices.
It is obvious that the devices with the later versions of operating systems installed on them are better suited to actively working online. Unfortunately, more active web surfing often leads users to sites hosting malicious content. More than one half of all malware detected on user smartphones turned out to be SMS Trojans, i.e. malicious programs that steal money from victims' mobile accounts by sending SMS messages to premium rate numbers.
To summarise, attacks of cybercriminals in Q3 most commonly targeted Android versions 2.3.6 Gingerbread and 4.0.4 Ice Cream Sandwich. Attackers are sufficiently good at bypassing restrictions on installing software from untrusted sources, primarily using social engineering techniques.
In the wild, Trojans that use a variety of methods to steal money from mobile users' accounts are the most widespread, although they are clearly being gradually replaced by more sophisticated versatile Trojans. Online attacks primarily involve various exploits that allow attackers to download malware onto victims' computers during drive-by attacks without having to resort to social engineering.
...
Madi, Gauss, Flame: Year's most sophisticated malware
Image: Workers are pictured beneath clocks displaying time zones in various parts of the world at an outsourcing centre in Bangalore.Photographs: Vivek Prakash/Reuters
The successful use of exploits is reliant on the presence of vulnerabilities in the code of popular applications installed on user machines. Java vulnerabilities were exploited in more than 50 per cent of all attacks.
According to Oracle, different versions of this virtual machine are installed on more than 1.1 billion computers. Importantly, updates for this software are installed on demand rather than automatically, increasing the lifetime of vulnerabilities. In addition, Java exploits are sufficiently easy to use under any Windows version and, with some additional work by cybercriminals, as in the case of Flashfake, cross-platform exploits can be created.
This explains the special interest of cybercriminals in Java vulnerabilities. Naturally, most detections are triggered by various exploit packs. A number of vulnerabilities that cybercriminals were quick to take advantage of were discovered in Q3. CVE-2012-1723, discovered in July, is an error in the HotSpot component, by exploiting which attackers can execute their class, bypassing the sandbox provided by the Java virtual machine.
Another vulnerability, CVE-2012-4681, was found in late August. Exploits for this vulnerability were first used in targeted attacks, but were quickly included in popular exploit packs.
...
Madi, Gauss, Flame: Year's most sophisticated malware
Image: Women use smartphones in front of the Trevi Fountain in Rome.Photographs: Tony Gentile/Reuters
Kaspersky Lab products successfully detected them using the Advanced Exploit Protection technology. Attacks via Adobe Reader rank second, accounting for a quarter of all attacks blocked. The popularity of exploits for Adobe Reader is gradually declining due to a realtively simple mechanism that ensures their detection, as well as to automated updates introduced in the latest versions of the Reader.
The geographic sources of web attacks were determined by comparing the domain name with the actual IP address where a specific domain is located, and determining the location of that IP address. Just 10 countries worldwide host 86 per cent of the web resources used to spread malware.
For the second quarter running this figure has climbed by a single percentage point. There is a new leader among countries hosting malicious content: Russia (23.2 per cent) has overtaken the US (20.3 per cent). In the last three months, the proportion of malicious hosts in Russia has dramatically increased (+8.6 percentage points); at the same time, the fall in the US share (-9.7 percentage points) has almost mirrored Russia's rise.
The number of malicious hosts in the Netherlands has also risen (+5.8 percentage points). Sixty per cent of all malicious content is located in the top three countries - Russia, the US and the Netherlands.
...
Madi, Gauss, Flame: Year's most sophisticated malware
Image: Tourists use an iPad tablet in front of Rome's ancient Colosseum.Photographs: Tony Gentile/Reuters
Without effective action from law enforcement agencies and hosting providers, this situation is likely to continue for several more months. There were no significant changes among the other countries in the Top 10, apart from the UK's share falling by 2.6 percentage points.
In the previous quarter, the top 20 consisted exclusively of countries from the former Soviet Union, Africa and SE Asia. This time, two Southern European countries are on the list, namely Italy (36.5 per cent) and Spain (37.4 per cent).
All these countries can be divided into four groups. The Maximum risk group includes countries where more than 60 per cent of users encountered malware at least once while online. In Q3, Tajikistan (61.1 per cent) found itself in this category, displacing Russia (58 per cent) from the leader's position.
The high risk group includes countries where 41 per cent to 60 per cent of users encountered online malware at least once. This group includes 10 countries from the top 20, eight countries fewer than in the last quarter. Along with Russia (58 per cent), this group includes Kazakhstan (54.9 per cent), Belarus (49.6 per cent) and Ukraine (46.1 per cent).
The moderate risk group (21-40 per cent) includes 99 countries, including India (38.4 per cent), Spain (37.4 per cent), Italy (36.5 per cent), Lithuania (33.5 per cent), China (33.4 per cent), Turkey (33.3 per cent), the US (32.4 per cent), Brazil (32.9 per cent), the UK (30.2 per cent), Belgium (28.3 per cent) and France (28.2 per cent).
...
Madi, Gauss, Flame: Year's most sophisticated malware
Image: Woman looks at her iPad tablet in Milan, Italy.Photographs: Stefano Rellandini/Reuters
The low risk group includes 27 countries where between 10.6 per cent and 21 per cent of users have encountered online malware. The safest surfing was in Japan (13.6 per cent), Denmark (17.7 per cent), Taiwan (15.4 per cent), Hong Kong (19.3 per cent), Luxembourg (19.7 per cent), Slovakia (20.7 per cent) and Singapore (20.9 per cent).
It should be noted that African countries are in the safest web surfing group. The low level of online attacks is due to the fact that Internet usage remains underdeveloped in these countries. This hypothesis is supported by the fact that the situation with local infections in these countries is far from healthy.
On average in Q3 2012, 36.7 per cent of KSN users' computers were attacked at least once while surfing online. That average is three percentage points less than the previous quarter.






article